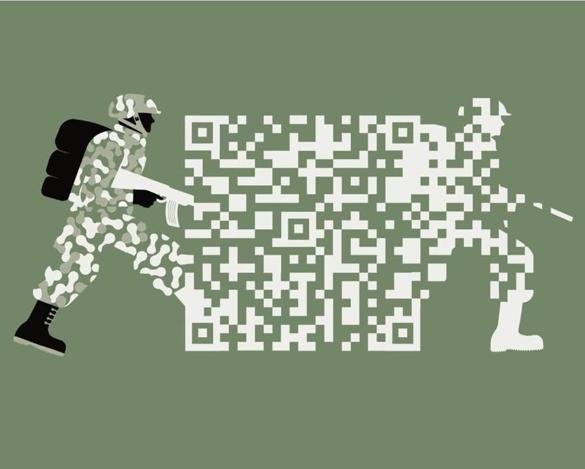
Nuke the Hackers: In Defense of 'Traditional Responses' to Cyber Warfare

EU to Declare Cyber-Attacks "Act of War"
At the end of last month, the EU drafted a diplomatic response framework to recent cyber attacks against European and Western infrastructure. This was a response largely to the effect that WannaCry attacks had on NHS systems, crippling healthcare networks nationwide for a significant period of time.
Nation state actors have stepped up activities in the online domain, between WannaCry, @theshadowbrokers dump of deeply classified national security information, and WikiLeaks dumping of CIA hacking tools. This escalation of attacks in cyberspace is largely parallel to an overall escalation in 'traditional' attacks worldwide, whether it be terrorism, traditional espionage, or violent crime.
Should we react the same way to a cyber attack on national infrastructure as we would if there were a 'traditional' physical attack? The EU decision has sparked intense debate online, with reactions ranging from exasperated acceptance of an action that many viewed as too little too late, to alarmist reactions of abhorrence to the idea of putting lead in head for DDoS'ing a government website.
In this article, I post in defense of a traditional response to Cyber Attacks. My reasoning is that most negative response to this draft framework is overly alarmist, that it could be tactically and strategically important to physically respond to cyber attacks, and that the alternative could result in a further escalation of cyber offensive campaigns resulting from inadequate responses.
Alarmism and Hyperbole

After the draft was released, many of the responses were extremely alarmist. There were those who thought that traditional response immediately meant mortar barrages and tanks knocking down your wall, and that the actors in question would be teenagers in mother's basements. Aside from how old the pimply teen hacker in mom's basement prejudice has gotten, these statements were blatantly alarmist and based more in hyperbole than in reality.
Physical responses to cyber attacks would be appropriately scaled to the target. We're not talking about sending Seal Team 6 to rural UK to take down a low-level card thief. We're talking about diplomatic pressure against nation-state actors and the possibility of a declaration of war in reaction to a catastrophic attack against state infrastructure.
We're living in a world where Russia has already turned the lights off in Ukraine during a physical invasion. The same world where Western nuclear infrastructure has been increasingly targeted for attack. Stuxnet, the worm that ruined Iran's nuclear program, is over 7 years old this year. This is not a cyber domain ruled over by pimply teens in hoodies, and it's time the world recognized that the web is being utilized by very dangerous actors that hold nation-state funds. These actors have one hand on the keyboard and the other hand on the missile silos, not in a bag of Cheetos. The sooner the world recognizes that hacking has moved past its old definition of fun-loving young adults and teenagers looking for a challenge, and is now a new wartime domain, the better.
Response scaleability is an obvious consideration in this issue, but the idea that the tanks would roll in after a minor DDoS attack is laughable at best. Declarations of War are diplomatic gambling pieces before they are military responses. The possibility of a declaration of war is a potential deterrent to preemptive offensive cyber activities. If anything, the deterrent possibility of this framework ensures more of a possibility of a diplomatic action than military, as it would bring parties to the table before they take action in the cyber domain.
Declaration of war has already been discussed as a reaction to a catastrophic cyber attack. Military response was discussed in some circles as a possible reaction for the attacks against the Ukraine, and were discussed further as a result of the WannaCry attack against NHS. WikiLeaks has been classified as a foreign agent against the US and other nations, giving them the same status as a military intelligence official. This diplomatic framework was more of a formalization than a new step.
Tactical and Strategic Importance

The tactical and strategic importance of this decision cannot be overstated. Tactically, a short-term plan of response after a cyber attack is already an important aspect of incident response, but now that targets of cyber attacks include critical infrastructure and nation-state assets, a physical response should be regarded as part of the incident response plan as well, on both a tactical and strategic level.
In an increasingly interconnected domain, where the power grid is connected to the same network that your grandmother's Facebook site is hosted on, cyber attacks have a real-world effect. The Ukranian power grid attack turned the lights off to the majority of the country. If the target were New York City, this kind of preemptive attack could precede a physical invasion. During the winter time, a widespread power outage could cost lives in colder regions, as it did in the Northeastern power outage in 2003 which claimed 11 lives.
A quick tactical response to a critical attack quite literally could save lives. It is much more difficult to attribute a cyber attack compared to a traditional attack. There are no heat signatures or smoke trails like there are in missile attacks, no smoking gun to look for aside from various technical signatures. Attribution is an obvious precursor to any kind of response, whether it be diplomatic, economic, or military. While it is one of the most difficult things in the cyber domain, an adequate incident response team could supply attribution in a short enough timeline to respond tactically to an event.
In the event that critical information is stolen, a tactical, short term response would be critical to retrieve stolen data before it is propagated or analyzed for use in intelligence activities. The gathering of intelligence is useless if the response is timely enough to cut off the analysis phase. Strategic response to the theft of critical information would entirely nullify the theft, actually making it extremely costly for the actor. This is like catching a thief who stole weapons from a pawn shop before they even have a chance to use or sell the weapon. You catch the perpetrator red handed with the 'goods', ensure that the stolen goods are never utilized, and impose a price on the actor before they can capture a reward for the theft.
Strategically, the long term effect of traditional response to cyber attacks is that it imposes a higher cost for the attacks and ensures a lower reward. Over the long term, the deterrent is even more effective. Imposing higher cost and lower reward for a certain action is the basis of most diplomacy. If actors knew that the result of a cyber attack was armed specialists knocking on the door, all of a sudden they think twice before pressing Enter.
The Alternative: Limited Response to Cyber War
Limiting the response to cyber attacks can be extremely dangerous. When a nation takes the stand and says that long-term false peace is more important than ensuring safety, sovereignty, and security, this ensures that the actors will continue to reap rewards with very little personal cost. If you were told that you could walk into a bank and take as much money and gold as you could carry, with a promise of no legal response, it is very unlikely that most of you would pass up that offer. It is the same with all things. Ensuring a nation-state actor can reap rewards without a cost promises the continuation of offensive action.
The current consensus is economic and diplomatic responses to cyber offensive operations. After the attribution of WannaCry to North Korean state actors, the US and others slapped (more) economic sanctions on the Hermit Kingdom. Economic sanctions hadn't worked to deter their nuclear program, and likely did even less to the cyber ransom hunters that set the world ablaze during the WannaCry plague. An inadequate cost is a step in the right direction compared to no response, but often isn't far enough.
Russia invaded a sovereign nation and turned off their lights. They likely hacked a democratic process and chose the leader of the free world. Economic sanctions are not an adequate response to the invasion of a nation or a democratic election. I don't believe a bombing run should be launched, but I also don't believe the military option should ever be taken off the table when the risk-reward ratio is so skewed without it.
---------------------
Like the post? I run this threat intelligence blog on Steemit and offer the content free of charge. If you're a Steemit user, you know that upvoting, which you do for free, magically puts a couple cents in my pocket. Maybe I'll buy a pack of gum with last week's earnings, but it all depends on your help. Not a Steemit user? My biggest metric of success is my viewership. If I don't make a cent but my content reaches a wide audience, that means my product is valuable and my efforts are worthwhile. Therefore, give me a share on your social media of choice, follow me on Steemit for more threat intel posts, and follow me on Twitter to see stupid memes and get updates when I post.
Hi! I am a robot. I just upvoted you! I found similar content that readers might be interested in:
https://gizmodo.com/report-donald-trump-will-order-military-to-begin-discr-1798376119
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit
Yeah you're way off on that one my robot friend. Thanks for the vote though.
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit
This is an interesting question. US reaction to 'traditional' physical attacks are many times not supported in real proof about the origin or even the reality of such attacks. A recent example being the chemical attack attributed to Assad, which Trump responded by bombing a Syrian Arab Army air base, killing a number of soldiers.
History tells us very clearly that when the US wants to attack some nation, generally in the Third World, it will basically use any excuse at hand, your perspective suggest a new kind of excuse, perhaps even easier to use, due to its nature and how hard it is to discover its origin without a doubt.
The Russian 'hacking' affair is months old and as you wrote: "they likely hacked a democratic process"... still not a sure thing. If they accuse any country of hacking with (sometimes anonymous) intelligence claims that show no proof, who will stop them, the press?
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit
The argument in this post sounds nice, but it falls apart when it meets reality.
The problem with the internet is that now, everyone is right next door.
There is no Poland in between. Physically, the attacker and the victim could be anywhere in the world, on the internet, they share a wall in their flats.
Most of the dangerous hacking is happening at the behest of big govern-cement agencies. It isn't a bunch of kids anymore. It is big interests with big money. Enough money to bribe, jail, turn friend on friend, and hire any number of "men in black" to come knock on your door in the middle of the night.
The danger is that we live in a technical age with very few people being technically savvy. All of those DHS hospitals, why do they have those computers connected to the internet? All buildings with any security necessities, should have two networks. One for all the people going to facebook, and one for all the internal machines to talk to each other. And there should be no connection between the systems.
But that would cost too much, everyone complains. With BRIX costing $300 and tablets $40, this is not an argument, this is just bureaucrats being cheap.
Further, winders is compromised. No one with any security need to should touch the thing.
So, we live in a world, where everyone lives next door to everyone else, and almost everyone leaves their doors open.
And the most important piece, is that armed responses to cyber attacks already happens. They are just done quiet like by the Cocain Import Agency and its foreign cohorts. But, these responses aren't meant to stop them, they are used to subvert them.
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit
Curated for #informationwar (by @openparadigm)
Relevance:Modalities of war
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit
Congratulations @odinthelibrarian! You have received a personal award!
Click on the badge to view your Board of Honor.
Do not miss the last post from @steemitboard!
Participate in the SteemitBoard World Cup Contest!
Collect World Cup badges and win free SBD
Support the Gold Sponsors of the contest: @good-karma and @lukestokes
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit
Congratulations @odinthelibrarian! You received a personal award!
You can view your badges on your Steem Board and compare to others on the Steem Ranking
Vote for @Steemitboard as a witness to get one more award and increased upvotes!
Downvoting a post can decrease pending rewards and make it less visible. Common reasons:
Submit